VMware has released VMware Horizon 7.3.1 and Horizon Client 4.6! With this new release, Horizon 7.3 enhances key platform features, including Horizon Virtualization Pack for Skype for Business, VMware Instant Clone Technology and the Horizon Help Desk Tool.
Many new items have been introduced, such as HTML5 video redirection support for the Chrome browser and the ability to configure Windows Start menu shortcuts for desktop and application pools using the Horizon Administrator console. As always, you can count on increased operating system support for virtual desktops and clients.
Here is an overview of the new features:
VMware Horizon 7.3 Server Enhancements
Horizon Help Desk Tool
- Displays application process resources with reset control
- Role-based access control for help desk staff
- Activity logging for help desk staff
- Displays Horizon Client information
- Granular logon time metrics
- Blast Extreme display protocol metrics
Instant Clone Technology
- Instant-clone desktops can now use dedicated assignment to preserve the hostname, IP address and MAC address of a user’s desktop
- Windows Server OS is now supported for desktop use
- Instant clones are now compatible with Storage DRS (sDRS)
- If there are no internal VMs in all four internal folders created in vSphere Web Client, these folders are unprotected, and you can delete them
- IcUnprotect.cmd utility can now unprotect or delete template, replica or parent VMs or folders from vSphere hosts
Windows Start Menu Shortcuts Created Using the Admin Console
- Create shortcuts to Horizon 7 resources:
- Published applications
- Desktops
- Global entitlements
Cloud Pod Architecture Scale
- Total session limit is increased to 140,000
- The site limit is now seven
VMware Horizon Apps
- This update makes Horizon Apps easier to use and allows the administrator to restrict entitlements
- Restrict access to desktop and application pools from specific client machines
Resiliency for Monitoring
- If the event database shuts down, Horizon administrator maintains an audit trail of the events that occur before and after the event database shutdown
Database Support
- Always-On Availability Groups feature for Microsoft SQL Server 2014
ADMX Templates
- Additional GPO settings for ThinPrint printer filtering, HTML5 redirection and enforcement of desktop wallpaper settings
Remote Experience
Horizon Virtualization Pack for Skype for Business
- Multiparty audio and video conferencing
- Horizon 7 RDSH support
- Windows Server 2008 R2
- Windows Server 2012 R2
- Forward Error Correction (FEC)
- Quality of Experience (QOE) metrics
- Customized ringtones
- Call park and pickup
- E911 (Enhanced 911) support, to allow the location of the mobile caller to be known to the call receiver
- USB desktop-tethering support
- Horizon Client for Linux support for the following Linux distributions:
- Ubuntu 12.04 (32-bit)
- Ubuntu 14.04 (32 & 64-bit)
- Ubuntu 16.04 (64-bit)
- RHEL 6.9/CentOS 6.x (64-bit)
- RHEL 7.3 (64-bit)
- SLED12 SP2 (64-bit)
Additional NVIDIA GRID vGPU Support
- Support for the Tesla P40 graphics card from NVIDIA
HTML5 Video Redirection
- View HTML 5 video from a Chrome browser and have video redirected to the client endpoint for smoother and more efficient video playback
Performance Counter Improvements
- Windows agent PerfMon counters improvements for Blast Extreme sessions: imaging, audio, client-drive redirection (CDR), USB and virtual printing
Linux Virtual Desktops
- KDE support: Besides RHEL/CentOS 6.x, the KDE GUI is now supported on RHEL/CentOS 7.x, Ubuntu 14.04/16.04 and SUSE Linux Enterprise Desktop 11 SP4
- MATE interface is now supported on Ubuntu 14.04 and Ubuntu 16.04
- Blast Extreme Adaptive Transport is now supported for Linux desktops
- vGPU hardware H.264 encoder support has been added
USB Redirection
- USB redirection is supported in nested mode
ThinPrint Filtering
- Administrators can filter out printers that should not be redirected
Horizon Client 4.6 Updates
Security Update
- All clients have been updated to use SHA-2 to prevent SHA-1 collision attacks
Session Pre-launch
- Session pre-launch is now extended to both Horizon Client for macOS and Horizon Client for Windows
Apteligent
- Integration of Apteligent crash log
Blast Extreme
- Improvements in Blast Extreme Adaptive Transport mode for iOS and macOS
- User can change Blast Extreme settings without having to disconnect
Horizon Client 4.6 for Windows
- Support for UNC path with CDR
Horizon Client 4.6 for macOS
- Support for macOS Sierra and macOS High Sierra
- Selective monitor support
- Norwegian keyboard support
Horizon Client 4.6 for iOS
- CDR support with drag and drop of files in split view
- iOS split keyboard enhancement
- iOS UI updates
Horizon Client 4.6 for Android
- Android Oreo support
- Manage the Horizon server list with VMware AirWatch
- Simple shortcuts
- External mouse enhancements
- Real-Time Audio-Video (RTAV) support for Android and Chrome OS
Horizon Client 4.6 for Linux
- Blast Extreme Adaptive Transport support
Horizon Client 4.6 for Windows 10 UWP
- Network recovery improvements
Horizon HTML Access 4.6
- HTML Access for Android with a revised UI
- Customization of HTML Access page
Horizon Help Desk Tool
The Horizon Help Desk Tool provides a troubleshooting interface for the help desk that is installed by default on Connection Servers. To access the Horizon Help Desk Tool, navigate to https://<CS_FQDN>/helpdesk, where <CS_FQDN> is the fully qualified domain name of the Connection Server, or click the Help Desk button in the Horizon Administrator console.

The Help Desk Tool was introduced in Horizon 7.2 and has been greatly expanded upon in the Horizon 7.3 release.
Help Desktop Tool features with Horizon 7.2:
- Virtual machine metrics
- Remote assistance
- Session control (restart, logoff, reset, and disconnect)
- Sending messages
Additional features with Horizon 7.3:
- Display application process resources with reset control
- Role-based access control for help desk staff
- Activity logging for help desk staff
- Granular login time metrics
- Display Horizon Client information
User Session Details
The user session details appear on the Details tab when you click a user name in the Computer Name option on the Sessions tab. You can view details for Horizon Client, the VDI desktop or RDSH-published desktop, CPU and memory stats, and many other details.
- Client version
- Unified Access Gateway name and IP address
- Logon breakdown (client to broker):
- Brokering
- GPO load
- Profile load
- Interactive
- Authentication

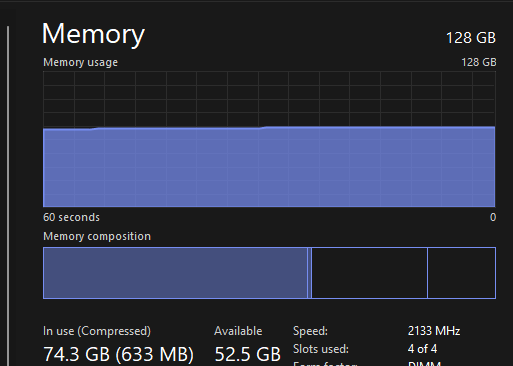
Blast Extreme Metrics
Blast extreme metrics that have been added include estimated bandwidth (uplink), packet loss, and transmitted and received traffic counters for imaging, audio, and CDR.
Note the following behavior:
- The text-based counters do not auto-update in the dashboard. Close and reopen the session details to refresh the information.
- The counters for transmitted and received traffic counters are accumulative from the point the session is queried/polled.
Blast Extreme Metrics for a Windows 10 Virtual Desktop Session

Display and Reset Application Processes and Resources
This new feature provides help desk staff with a granular option to resolve problematic processes without affecting the entire user session, similar to Windows Task Manager. The session processes appear on the Processes tab when you click a user name in the Computer Name option on the Sessions tab. For each user session, you can view additional details about CPU- and memory-related processes to diagnose issues.

Role-based Access Control and Custom Roles
You can assign the following predefined administrator roles to Horizon Help Desk Tool administrators to delegate the troubleshooting tasks between administrator users:
- Help Desk Administrator
- Help Desk Administrator (Read Only)
You can also create custom roles by assigning the Manage Help Desk (Read Only) privilege along with any other privileges based on the Help Desk Administrator role or Help Desk Administrator (Read Only) role.

Members of the Help Desk Administrators (Read Only) role do not have access to following controls; in fact, functions such as Log Off and Reset are not presented in the user interface.

Watch this brief demonstration video of the Horizon Help Desk Tool to see it in action:
Horizon Virtualization Pack for Skype for Business
You can now make optimized audio and video calls with Skype for Business inside a virtual desktop without negatively affecting the virtual infrastructure and overloading the network.
All media processing takes place on the client machine instead of in the virtual desktop during a Skype audio and video call.

New support with many expanded features for the Horizon Virtualization Pack for Skype for Business can be found in Horizon 7.3 and Client 4.6.
New Features
Horizon Virtualization Pack for Skype for Business offers the following supported features:

System Requirements
The following table outlines the system requirements for the new release:

Supported Clients
The following table provides the list of support Horizon clients:

Start Menu Shortcuts Configured Through the Admin Console
This feature improves the user experience by adding desktop and application shortcuts to the Start menu of Windows client devices.
You can use Horizon Administrator to create shortcuts for the following types of Horizon 7 resources:
- Published applications
- Desktops
- Global entitlements
Shortcuts appear in the Windows Start menu and are configured by IT. Shortcuts can be categorized into folders.

Users can choose at login whether to have shortcuts added to the Start menu on their Windows endpoint device.

Watch this brief demonstration video of the new Desktop and Apps Shortcuts feature to see it in action:
Dedicated Desktop Support for Instant Clones
Upon the initial release of instant clones in Horizon 7, we supported floating desktop pools and assignments only. Further investments have been made to Instant Clone Technology that add support for dedicated desktop pools. Fixed assignments and entitlements of users to instant-clone machines is now provided as part of Horizon 7.3.
Dedicated instant-clone desktop assignment means that there is a 1:1 relationship between users and desktops. Once an end user is assigned to a desktop, they will consistently receive access to the same desktop and corresponding virtual machine. This feature is important for apps that require a consistent hostname, IP address, or MAC address to function properly.
Note: Persistent disks are not supported. Fixed assignments to desktops does not mean persistence for changes. Any changes that the user makes to the desktop while in-session will not be preserved after logoff, which is similar to how a floating desktop pool works. With dedicated assignment, when the user logs out, a resync operation on the master image retains the VM name, IP address, and MAC address.

Support for the Tesla P40 Graphics Card from NVIDIA
VMware has expanded NVIDIA GRID support with Tesla P40 GPU cards in Horizon 7.3.

HTML5 Video Redirection
This feature provides the ability to take the HTML5 video from a Chrome (version 58 or higher) browser inside a Windows VDI or RDSH system and redirect it to Windows clients. This feature uses Blast Extreme or PCoIP side channels along with a Chrome extension.
The redirected video is overlaid on the client and is enabled as well as managed using GPO settings.
Benefits include:
- Supports generic sites such as YouTube, without requiring a server-side plugin.
- Provides smooth video playback comparable to the native experience of playing video inside a browser on the local client system.
- Reduces data center network traffic and CPU utilization on the vSphere infrastructure hosts.

Improved USB Redirection with User Environment Manager
The default User Environment Manager timeout value has been increased. This change ensures that the USB redirection Smart Policy takes effect even when the login process takes longer than expected.
With Horizon Client 4.6, the User Environment Manager timeout value is configured only on the agent and is sent from the agent to the client.
You can now bypass User Environment Manager control of USB redirection by setting a registry key on the agent machine (VDI desktop or RDSH server). This change ensures that smart card SSO works on Teradici zero clients. Note: Requires a restart.
HKLM\Software\VMware, Inc.\VMware VDM\Agent\USB uemFlags (REG_DWORD 1)
Blast Extreme Performance Counter Improvements
The Windows Agent PerfMon counters for the Blast Extreme protocol have been improved to update at a constant rate and to be even more accurate.
Counters include:
- Imaging
- Audio
- CDR
- USB
- Virtual printing

Linux Virtual Desktops
Features and functions for Horizon 7 for Linux virtual desktops have been expanded:
- KDE support – Besides RHEL/CentOS 6.x, the KDE GUI is now supported on RHEL/CentOS 7.x, Ubuntu 14.04/16.04, SUSE Linux Enterprise Desktop 11 SP4.
- Support for the MATE interface on Ubuntu 14.04, Ubuntu 16.04.
- Blast Extreme Adaptive Transport support.
- vGPU hardware H.264 encoder support.

USB Redirection Support in Nested Mode
The USB redirection feature is now supported when you use Horizon Client in nested mode. When using nesting–for example, when opening RDSH applications from a VDI desktop–you can now redirect USB devices from the client device to the first virtualization layer and then redirect the same USB device to the second virtualization layer (that is, nested session).
Filtering Redirected Printers
You can now create a filter to specify the printers that should not be redirected with ThinPrint. A new GPO ADMX template (vmd_printing_agent.admx) has been added to enable this functionality.
By default, the rule permits all client printers to be redirected.
- Supported attributes:
- PrinterName
- DriverName
- VendorName
- Supported operators:
- Supported searching pattern is a regular expression.

Blast Extreme Improvements in CPU Usage
Now even lower CPU usage is achieved with adaptive Forward Error Correction algorithms. This clever mechanism decides how to handle error correction, lowering CPU usage within virtual desktop machines as well as on client endpoint devices.
Blast Extreme Adaptive Transport Side Channel
New support has been added for Blast Extreme Adaptive Transport side channels for USB and CDR communications. Once enabled, TCP port 32111 for USB traffic does not need to be opened, and USB traffic uses a side channel. This feature is supported for both virtual desktops and RDS hosts.
- Feature is turned off by default.
- Enable the feature through a registry key: HKEY_LOCAL_MACHINE\SOFTWARE\VMware, Inc.\VMware Blast\Config\UdpAuxiliaryFlowsEnabled 1

Entitlement Restrictions Based on Machine Name
This feature allows IT administrators to restrict access to published applications and desktops based on both client computer and user. With client restrictions for RDSH, it is now possible to check AD security groups for specific computer names. Users only have access to desktops and apps when both the user and the client machine are entitled. For this release, the feature is supported only for Windows clients and works with global entitlements.

Pre-Launch Improvements
Pre-launch provides the ability to launch an empty (application-less) session when connecting to the Connection Server. The feature is now also available to Windows clients, in addition to macOS.
Also, it is no longer necessary to manually make changes to the client settings. You can configure automatic reconnection.

Blast Extreme Adaptive Transport Mode for iOS and macOS
With prior client releases, users were required to configure their Blast Extreme settings before they connected to the Connection Server. After a connection was established, the options to change the Blast Extreme setting—which included H.264, Poor, Typical, and Excellent—were unavailable.
With this release, users can change the network condition setting from Excellent to Typical or the reverse while inflight to sessions. Doing so also changes the protocol connection type between TCP (for Excellent) and UDP (for Typical).
Note: End users will not be able to change the network condition setting if Poor is selected before establishing a session connection.

Horizon Client for Windows
Horizon Client 4.6 updates include:
- Additional command-line options for the new client installer – When silently installing the Windows client, using the /s flag, you can now also set:
- REMOVE-SerialPort,Scanner – Removes the serial port, scanner, or both.
- DESKTOP_SHORTCUT-0 – Installs without a desktop shortcut.
- STARTMENU_SHORTCUT-0 – Installs without a Start menu shortcut.

- Support for UNC paths with client drive redirection (CDR):
- Allows remote applications to access files from a network location on the client machine. Each location gets its own drive letter inside the remote application or VDI desktop.
- Folders residing on UNC paths can now be redirected with CDR, and get their own drive letter inside the session, just as any other shared folder.

Horizon Client for macOS
Horizon Client 4.6 updates include:
- Apple macOS High Sierra day 0 support.
- Users can select which monitors to use for VDI sessions and which to use for the local system.
- Norwegian keyboard support and mappings are now available
Horizon Client for iOS
Horizon Client 4.6 updates include:
- iOS 11 support
- iOS split keyboard update – Removes the middle area in the split keyboard for a better view of the desktop
- New dialog box for easy connection to a Swiftpoint Mouse
Horizon Client for Android
Horizon Client 4.6 updates include:
- Android 8.0 Oreo support.
- Server URL configuration – Allows administrators to configure a list of Connection Servers and a default Connection Server on Android devices managed by VMware AirWatch.
Android and Chrome OS Client Updates
Horizon Client 4.6 for Android and Horizon Client 4.6 for Chrome OS updates include:
- Simple shortcuts – Users can right-click any application or desktop to add a shortcut to the home screen.
- Webcam redirection – Integrated webcams on an Android device or a Chromebook are now available for redirection using the Real-Time Audio-Video (RTAV) feature.
HTML Access
HTML Access 4.6 updates include:
- HTML Access on Android devices – Though HTML Access has fewer features than the native Horizon Client, it allows you to use remote desktops and published applications without installing software.
- HTML Access page customization – Administrators can customize graphics and text and have those customizations persist through future upgrades.
Horizon Client for Linux
Horizon Client 4.6 updates include:
- Support for Raspberry Pi 3 Model B devices:
- ThinLinx operating system (TLXOS) or Stratodesk NoTouch operating system
- Supported Horizon Client features include:
- Blast Extreme
- USB redirection
- 264 decoding
- 8000Hz and 16000Hz audio-in sample rate
- RHEL/CentOS 7.4 support
Horizon Client for Windows 10 UWP
Horizon Client 4.6 updates include:
- Network recovery improvements – Clients can recover from temporary network loss (up to 2 minutes). This feature was already available for Windows, macOS, Linux, iOS, and Android, and is now available for Windows 10 UWP.
- Automatically reconnects Blast Extreme sessions
- Reduces re-authentication prompts
We are excited about these new features in Horizon 7.3.1 and the Horizon Client 4.6. We hope that you will give them a try.
You can download it here.
Like this:
Like Loading...
































You must be logged in to post a comment.